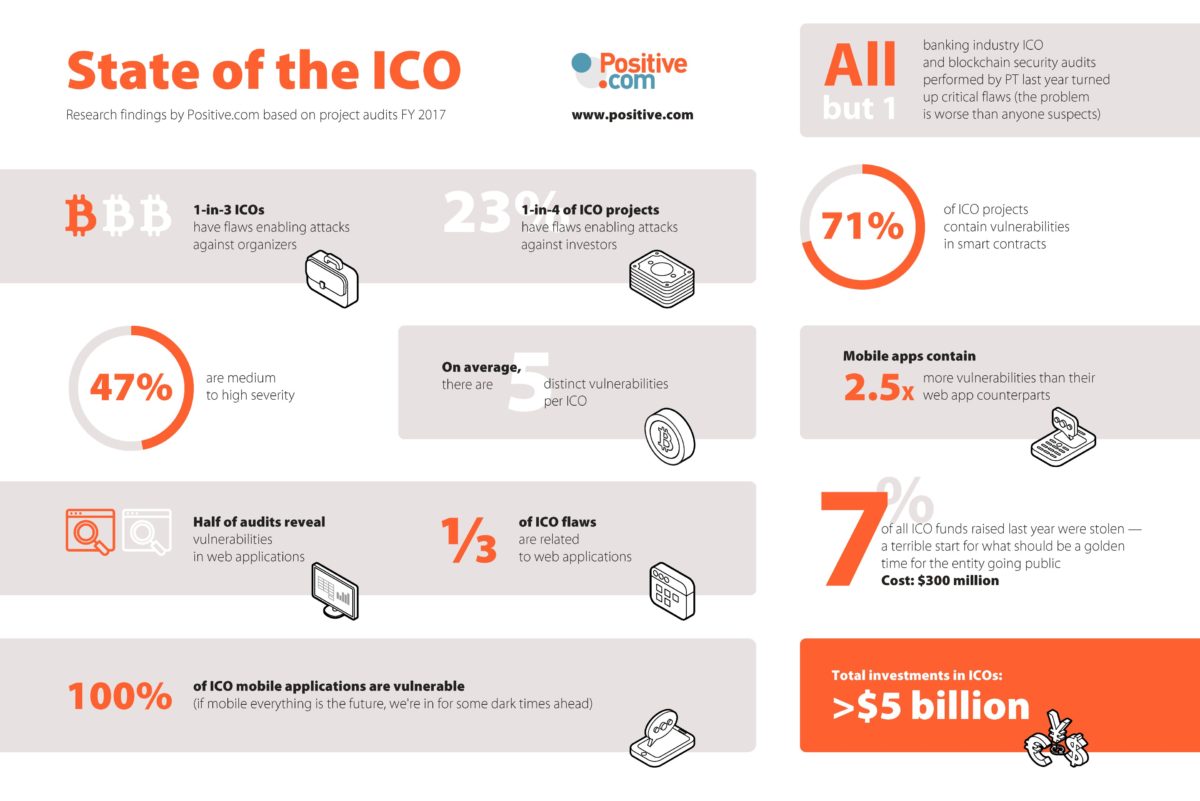
Positive.com’s specialist anti-fraud team found an average of five separate vulnerabilities in each project they examined in 2017, revealing the extent of risk for ICO management teams and investors alike. 47% of ICO vulnerabilities uncovered by Positive.com’s anti-fraud team were medium to high severity. Just one vulnerability is enough for attackers to steal investors’ money and do irreparable damage to corporate reputation.
According to various estimates, total investments in ICOs exceeded $5 billion in 2017, with the first quarter of 2018 showing no sign of slowdown. With large sums of money available, incentives for cybercriminals are high, and in fact, we saw 7% of all funds raised in ICOs last year stolen, to the value of $300 million. Of all the security audits conducted for Positive.com clients active in ICOs and blockchain deployment in the banking industry in 2017, only one did not contain any critical flaws.
Positive.com has launched the open beta phase of its unique Chainwatch product, which provides real-time monitoring and detection of attacks on ICO smart contracts and wallets. Currently in trial with customers, and the open beta phase making it open to the public, Chainwatch allows timely response to suspicious activity through predefined rules (blockchain metrics), which alert when a threshold is reached and an anomaly detected – such as abnormal money withdrawal. Early alerts to potentially fraudulent activity allow ICO organisers to take evasive action, such as withdrawing funds or warning investors to hold money transfer
Chainwatch is the only product that can monitor all Ethereum smart contracts in real-time, with automated alerts to owners and investors, meaning ICO organizers can take a proactive approach to security and monitor the load on the service. New checks are being added daily, but Chainwatch already detects key attack types, including Transaction Ordering Dependence (TOD), Reentrancy, Short Address Attacks and anomalous attacks.
Leigh-Anne Galloway, Cyber Security Resilience Lead at Positive.com said “In an ICO, time is of the essence, and short time frames mean that anticipating attacks well in advance is critical for avoiding financial losses. The latest figures have shown the rapidly increasing rate of crime and fraud on the cryptocurrency market, with cybercriminals recognising the opportunity presented by the dramatic rise of the cryptocurrency market in recent months. However, none of the ICOs protected by Positive.com fell victim to cyberattacks and all successfully completed their ICOs without incident.”
Positive.com found that 71% of tested projects contained vulnerabilities in smart contracts, the heart and soul of an ICO. Once an ICO starts, the contract cannot be changed and is open to everyone, meaning anyone can view it and look for flaws. Typically, vulnerabilities in smart contracts occur due to lack of programmer expertise and insufficient source code testing, with high-profile incidents, including the recent BatchOverFlow bug and the Parity Wallet vulnerability in late 2017. And one third of all ICO vulnerabilities detected by Positive.com experts were in smart contracts.
Half of audits revealed vulnerabilities in ICO web applications, a huge risk with unauthorised control of a website and its contents potentially causing multi-million dollar losses in just minutes.
The team found vulnerabilities were divided into five groups;
- Vulnerabilities allowing attacks against ICO organizers – in fact, Positive.com found that 1 out of 3 ICOs had flaws that enabled attacks against organizers. Attack strategies can include hijacking the email account of the ICO organizer, using information on social networks, gaining text message information from darknet merchants or social engineering techniques to bypass two-factor authentication, for example. Once the email account has been hijacked, attackers can reset the password for the ICO domain or web host, and subsequently replace the wallet address, for example as in an attack against Coindash.io, resulting in a $7 million loss.
- Vulnerabilities in smart contracts – typically, these would consist of non compliance with the ERC20 standard (the token interface for digital wallets and cryptocurrency exchanges), incorrect random number generation and incorrect scoping amongst others. Generally these vulnerabilities occur due to lack of programmer expertise and insufficient source code testing.
- Vulnerabilities in web applications – some of these involved the security of the blockchain itself and its backend implementation (for example with web3.js), whilst others are more general, including code injection, web server disclosure of sensitive information, insecure data transfer and arbitrary file reading.
- Vulnerabilities allowing attacks against investors – the risk of social engineering-based attacks can be mitigated by smart pre-planning by ICO teams, registering all possible versions of the project domain name, misspellings and signing up/registering names on social media accounts. And ICO teams should take notice of this — 23% of projects tested by Positive.com experts contained flaws that allow attacks against investors.
- Vulnerabilities in mobile applications – created by some ICO teams for investor convenience, the Positive.com team identified 2.5 times more vulnerabilities in ICO mobile apps than in ICO web applications. And alarmingly, vulnerabilities were detected in 100% of ICO mobile applications. The most common flaws found include insecure data transfer, storage of user data in backups and session ID disclosure. These flaws may be useful in gaining details about a project, its organizers and investors, prompting use by attackers in subsequent attacks.
Galloway continued: “The second a company goes public with an intention to do an ICO, it’s waving a huge flag to cyber criminals that it’s both valuable and also in a very vulnerable phase of its company growth. ICO teams have a responsibility to ensure their security posture is as robust as possible, from the development of the smart contract and web applications, to monitoring load once the ICO has begun and helping investors avoid phishing attacks.”